A Vendor Breach, an Education-Sector Phishing Wave, and Three Days to the Leak Deadline: The Canvas / Instructure Incident

Written by the Rafter Team
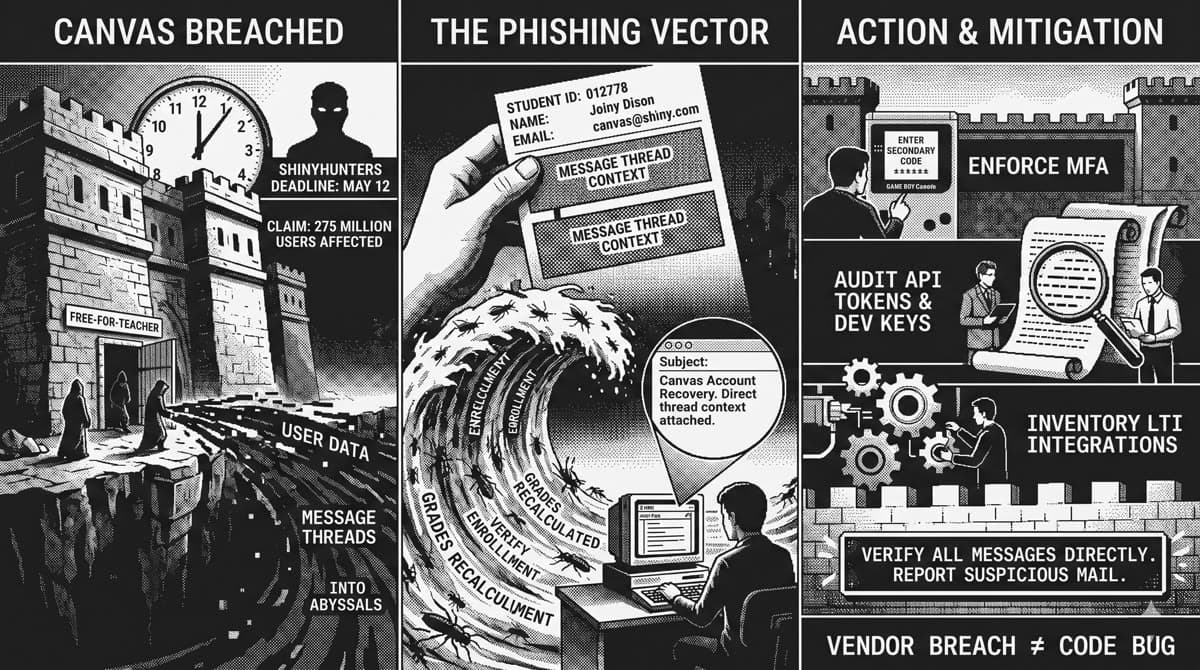
On April 29, 2026, Instructure detected unauthorized activity in Canvas, revoked the actor's access, hired a third-party forensic firm, and notified the FBI and CISA. The access path was tied to an issue in Free-For-Teacher accounts, Instructure's free tier for individual instructors, which was temporarily shut down. On May 7, the same actor returned and defaced login pages at multiple institutions, leading Instructure to take Canvas offline temporarily before bringing it back online the following day.
The hacking group ShinyHunters has claimed responsibility, says it accessed personal data on 275 million users across 8,809 schools, districts, universities, and online learning platforms, and has set a leak deadline of May 12, 2026 — three days from publication of this post — unless ransom demands are met.
Instructure's confirmed data scope is narrower than the attacker claims. Names, email addresses, student ID numbers, and messages between Canvas users at affected organizations. No evidence of password, date-of-birth, government ID, or financial data exposure. No evidence that data was taken during the May 7 defacement, though that investigation is ongoing.
A confirmed scope without passwords or payment data reads, on first pass, like a "could have been worse" outcome. For Canvas, the opposite is true.
If you are a student or faculty member at a school that uses Canvas, treat every Canvas-themed email through May as suspect. "Canvas account recovery," "your grades have been recalculated," "verify your enrollment," "finals login reset" are the lures to expect. Verify by going directly to your institution's Canvas portal — not by clicking a link in mail — and report suspicious messages to your school's IT or security team.
The timeline
April 29, 2026. Instructure detects unauthorized activity in Canvas. Access revoked, forensic firm engaged, law enforcement notified. The access path is "an issue related to our Free-For-Teacher accounts" — Instructure's free instructor tier — which is temporarily shut down as a containment measure.
May 5, 2026. Affected organizations are notified.
May 7, 2026. The same actor returns. Login pages at multiple institutions display an HTML-injected message from ShinyHunters, with TechCrunch confirming defaced portals at three separate schools. Instructure takes Canvas offline temporarily.
May 8, 2026. Canvas is brought back online with platform-wide protections, rotated internal keys, restricted token-creation pathways, revoked privileged credentials, and added monitoring.
May 12, 2026. ShinyHunters' stated deadline for releasing the data unless ransom demands are met.
The data
Instructure's published scope: "names, email addresses, student ID numbers, and messages among Canvas users." No evidence of password, DOB, government-ID, or financial-data access.
ShinyHunters' attacker claim, separately: 275 million users, 8,809 institutions. A list of affected institutions was reportedly shared with BleepingComputer. The Daily Pennsylvanian has reported more than 300,000 University of Pennsylvania users on the affected list.
Treat the attacker numbers as attacker claims. Treat the data scope as confirmed.
Why the narrow scope is the entire problem
A real student name, a real institutional email address, a real student ID number, and a real Canvas message thread between that student and an instructor is not an inert dataset. It is the highest-fidelity phishing corpus the education sector has ever seen leak in one pull.
A phishing email written using real Canvas thread context is a different threat model than one written from scratch. The attacker no longer has to guess what kind of message would feel natural in the recipient's inbox. They have a record of what did feel natural, and they can write into the same conversation register, citing a real assignment name, a real course code, a real instructor, and a real prior exchange. That gets through the human "wait, this feels off" check at materially higher rates than a generic "your account has been compromised, click here to reset" lure.
The risk concentrates around three reader profiles.
Faculty triaging end-of-semester mail
Final grades, late-submission requests, student appeals, and grade-change paperwork all spike in May. A "Re: your final exam reweighting" message that quotes a real prior thread, from a real student name, will be opened. A subset of those will be acted on without verification.
Students worried about specific outcomes
A "your grade has been recalculated" or "your enrollment has not been verified" message lands hardest on the people most worried about the underlying outcome. ShinyHunters' May 12 deadline aligns with the back half of finals season at the majority of named institutions for a reason.
AI inbox assistants
This is the part of the threat model that did not exist at this scale a year ago. Inbox-reading assistants — Gemini summarization, Apple Intelligence thread prioritization, Copilot mail integrations, MCP-fed agents on top of school mail accounts — are configured to weight signed senders heavily and to act on email content. A school-domain sender plus a Canvas-themed thread plus a verification link is precisely the configuration those agents are built to trust. They will summarize, prioritize, and in some cases follow the link in milliseconds, with no per-user pause.
This is the same trust-channel problem the Robinhood incident surfaced in late April, applied to the education sector at academic-calendar scale.
What this is not
It is not just a Canvas outage. Instructure's own update is unambiguous: unauthorized access, data exposure, and, on May 7, defacement. Treating it as a service-availability incident underestimates the downstream.
It is not a code bug your security team can scan for. The Free-For-Teacher access path is on Instructure's side. No amount of code scanning in a school's own repos catches a vendor's tier-permission bug. The honest read is that pre-merge scanning is not the line of defense that mattered here, and being honest about that matters more than positioning.
What scanning can address is your own product's analog of the same bug class. If you ship software with a free, trial, demo, or "lightweight" tier that touches any of the same identity primitives as your paid tier — accounts, tokens, integration keys, admin operations — that tier is a permission boundary that will be probed. It is the same class of finding Rafter's Code Analysis Engine looks for in admin-tier code: a privileged operation whose authorization scope does not match the tier of the caller. The Free-For-Teacher path is the canonical example you can point to in a design review for the next 18 months.
What to do this week
If you run Canvas at a school
Instructure's published guidance is the floor.
- Enforce MFA on every admin and developer-key holder.
- Audit every API token, OAuth grant, and developer key issued in the last six months. Rotate the privileged ones.
- Inventory LTI integrations.
- Pull the list of authorizations created from late April through May 7 and review for anything anomalous.
- Pull abnormal Canvas message exports from the same window.
- Prepare a targeted phishing-warning email for staff and students, dated before May 12, that names the leak deadline and tells recipients exactly how to verify Canvas-themed mail.
If you are a student or faculty member
Treat every Canvas-themed email through May as suspect. "Canvas account recovery," "your grades have been recalculated," "verify your enrollment," "finals login reset" are the lures to expect. Verify by going directly to your institution's Canvas portal, not by clicking a link in mail. Report suspicious messages to your school's IT or security desk.
If you build inbox-reading agents
Add a content-trust layer beneath the authentication-trust layer. Treat email body content as adversarial input even when the sender is verified, especially around late April through mid-June for any mailbox associated with one of the named institutions. SPF, DKIM, and DMARC tell you who sent the message. They do not tell you whether the content was composed by the school registrar or by an attacker working from a stolen Canvas thread.
Closing on the academic calendar
ShinyHunters did not pick May 12 by accident. The leak deadline lands inside finals window for the majority of named institutions. Whatever percentage of recipients normally squint at a phishing lure drops sharply during finals, and ShinyHunters' campaign — plus the second-order wave from anyone else who buys or scrapes the leak — is timed to that drop.
The shape of the breach is small. The shape of the corpus it produced is large. Three days to the deadline. The right move is the boring one: tell people now, in their own institution's voice, what to expect.
Further reading
- A Real Email From Robinhood Carrying Real Phishing — what happens when the trust signal a defender uses is exactly the signal the attacker mimics. Same trust-channel thesis, different sector.
- The Vercel / Context.ai Breach — vendor concentration as a single point of failure for downstream customers.
- Three Supply Chains, One Trust Relationship — when an attacker can pick which trust relationship to abuse, the defender has to harden all of them.
Sources
- Instructure — Security Incident Update & FAQs: https://www.instructure.com/incident_update
- AP News — Cyberattack on Canvas system causes chaos for students at thousands of schools: https://apnews.com/article/a0d7719689263e6b5f90d0e633391b5b
- TechCrunch — Hackers deface school login pages after claiming another Instructure hack: https://techcrunch.com/2026/05/07/hackers-deface-school-login-pages-after-claiming-another-instructure-hack/
- CNN — Canvas hack: What we know about apparent cyberattack that impacted thousands of schools: https://www.cnn.com/2026/05/07/us/canvas-hack-strands-college-students-finals-week
- DataBreaches.Net — Developing: ShinyHunters Hacks Instructure Again; Canvas Down: https://databreaches.net/2026/05/07/developing-shinyhunters-hacks-instructure-again-canvas-down/
- Times Higher Education — Personalised phishing attacks likely after global Canvas hack: https://www.timeshighereducation.com/news/personalised-phishing-attacks-likely-after-global-canvas-hack